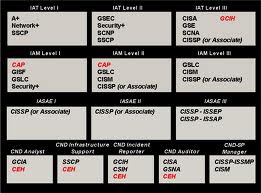
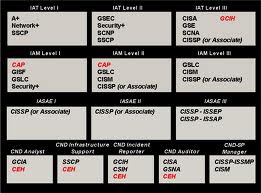
DoD 8570 Training in San Antonio, TX.
TechNow has developed a proven training program that brings the skillset to the certification process. TechNow is a mobile testing center that can deliver D0D 8570 training and the certification in one week. Our intergrated DoD 8570 training in San Antonio, TX incorporates hands on skills with testing objectives that produces an incredibly high pass rate. To learn more about our DoD 8570 training program click here
TechNow is a mobile Pearson VUE Authorized Testing Center, and we can provide the testing right after your certification prep class; thus ensuring a higher pass rate on the certification exams.
Technow is also a mobile Prometric Testing Center.
We can deliver the on-site training and test all in the same week.
For more information, call us today at 800-324-2294

Course Overview:
A skills focus enables the student to better absorb the subject matter and perform successfully on the job. This is not death by power point. The course is aligned with information assurance operators and executing hands-on labs to secure Windows systems. Lecture and labs start with quick review of Active Directory and group policy to enforce security mechanisms within the Windows architecture. Students then gain network experience and use sniffing to help exemplify the benefit of learning wired and wireless security configurations. PowerShell is made for SecOps/DevOps automation and students will learn to write PowerShell scripts to automate security operations and Desired State Configuration (DSC). The course concludes with exercising real attack strategies to demonstrate the effectives of properly securing your host.
Attendees to TN-969: Windows Security Administrator course will receive TechNow approved course materials and expert instruction.
Date/Locations:
No Events
Duration: 5 days
Course Objectives:
- Active Directory and BloodHound
- Security Controls
- PKI
- Encryption
- Wireless & Network Security and Hardening DNS
- 802.1x and Endpoint Protection
- Firewalls and VPN
- PowerShell Scripting
- JEA, DSC, Enterprise Security with PowerShell
- Windows Attack Strategies
Prerequisites:
- Security+
- Windows System Administration Skills
Comments
Latest comments from students
User: bbrabender
Instructor comments: Instructor was very knowledgeable and help more inexperienced users with concepts as well explaining in a way that can be understood.
Facilities comments: N/A
User: dale.r.anderson
Instructor comments: Instructor was well knowlegeable accross alot of domains.
Facilities comments: Pretty good
Liked the class? Then let everyone know!
Course Overview:
TechNow has worked worldwide enterprise infrastructures for over 30 years and has developed demos and labs to exemplify the techniques required to demonstrate technologies that effectively support CTI. This course integrates well with our courses TN-575: Open Source Network Security Monitoring and TN-865: Wireshark Network Traffic and Security Analysis .
TechNow develops Cyber Ranges and makes them available for conferences in support of annual meetings for Cyber Threat Response Teams. Developing scenarios and reacting to them appropriately is a big part of the value in understanding the contexts required to comprehend valuable CTI. As with many advanced TechNow security courses, there is a large hands-on ratio. This course helps Cyber Protection Teams (CPT), Defensive Cyber Operations (DCO), and Mission Defense Teams (MDT) to collect, analyze and apply targeted cyber intelligence to defensive operations in order to proactively act on and tune response to attacks by cyber adversaries. CPT, DCO, and MDT can take preemptive action by utilizing CTI, understanding CTI tools, techniques and procedures (TTPs) needed to generate and consume timely and relevant intelligence to improve resilience and prevention.
This course focuses on the collection, classification, and exploitation of knowledge about adversaries and their TTPs. . MDT puts us close the mission and helps define the internal context to be analyzed against the CTI. TechNow pushes the student to truly understand how to think about and use CTI to make a difference.
Attendees to TN-905: Cyber Threat Intelligence Analysis will receive TechNow approved course materials and expert instruction.
Date/Locations:
No Events
Course Duration: 5 days
Course Objectives:
- Learn to comprehend and develop complex scenarios
- Identify and create intelligence requirements through practices such as threat modeling
- Utilize threat modeling to drive intelligence handling and practices
- Breakdown tactical, operational, and strategic-level threat intelligence
- Generate threat intelligence to detect, respond to, and defeat focused and targeted threats
- How to collect adversary information creating better value CTI
- How to filter and qualify external sources, mitigating low integrity intelligence
- Create Indicators of Compromise (IOCs) in formats such as YARA, OpenIOC, and STIX
- Move security maturity past IOCs into understanding and countering the behavioral tradecraft of threats
- Breaking down threats mapped against their tradecraft to tweak IOCs
- Establish structured analytical techniques to be successful in any security role
- Learn and apply structured principles in support of CTI and how to communicate that to any security role.
Course Prerequisites:
Comments
Latest comments from students
Liked the class? Then let everyone know!