DoD 8570 Training
The Department of Defense requires that all information assurance personnel must become compliant with IT and security certification standards.
DoD 8570 training, also called Information Assurance training, is available through TechNow to provide you with the certification that is required. Your DoD 8570 training ( information assurance training ) at TechNow will provide you with all of the courses necessary to receive your DoD 8570.01-M certification.
Ongoing open enrollment through TechNow is available for our DoD 8570.01-M courses.
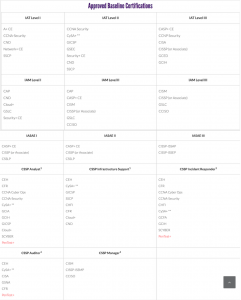
Please review the full & updated DoD approved IA baseline certifications aligned to each category & level of the IA workforce.
- CL-315: CCSP – Certified Cloud Security Professional Preparation Seminar
- CT-205: A+ Certification Course
- CT-208: A+ Extended Boot Camp
- CT-225: Network+
- CT-325: Security+
- CT-395: CySA+ Cybersecurity Analyst
- CT-425: CompTIA Advanced Security Practitioner (CASP+)
- TN-415: Computer Hacking Forensics Investigator (CHFI)
- TN-545: Certified Network Defender
- TN-555: Certified Ethical Hacker v13 (CEH)
- TN-715: Systems Security Certified Practitioner (SSCP)
- TN-812: Information Systems Security Engineering Professional (ISSEP)
- TN-813: Certified in Governance, Risk and Compliance (CGRC)
- TN-8150: CISSP Certification Preparation Seminar
- TN-822: Certified Information Systems Auditor (CISA) Seminar
- TN-825: Certified Information Security Manager (CISM) Seminar
- TN-835: Certified in Risk and Information Systems Control (CRISC) Preparation Seminar
- TN-865: Wireshark Network Traffic and Security Analysis
For further information or to schedule for classes, call us at 800-324-2294