Palo Alto Networks
CompTIA
Unix/Linux
Project Management
Virtualization/Cloud
Security
Cisco
Microsoft
Business
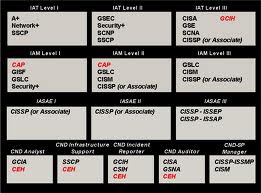
Dod 8140 Training
Programming
Specialized
Course Overview:
C-225: C++ Object Oriented Programming is a hands-on course that provides a complete introduction to the ANSI Standard C++ programming language, focusing on quickly developing the practical skills needed to create real-world solutions. Our hands-on labs are designed to promote retention and challenge students to apply their skills to new situations.
C++ is more than just C with classes. It is a whole new language with a structure similar to C, but with significant differences to warrant a complete course to cover its features.
Attendees to C-225: C++ Oriented Programming will receive TechNow approved course materials and expert instruction.
Dates/Locations:
No Events
Duration: 5 Days
Course Objectives:
- Classes
- Casting in C++
- Constructors & Destructors
- Class Methods & Data
- Inheritance
- Overloaded Functions
- Virtual Functions
- Overloaded Operators
- Pure Virtual Functions
- Exception Handling
- References & Constants
- Standard Template Library
- New and Delete
- STL Containers
Prerequisites:
- Students must possess basic C and OO competency or take PL-115: Fundamentals of Computer Programming & C-215 Introduction to C Programming.
Comments
Latest comments from students
User: christinehejnal
Instructor comments: The material was made clear, however I don't agree that she shouldn't have catered towards the people not taking the exam.
Facilities comments: The facilities were cold and very noisy, I found it hard to concentrate.
User: mamacker1
Instructor comments: Informative instructor. Definitely not monotone. I'd recommend it to my sister if I had one.
Liked the class? Then let everyone know!
DoD 8570 Training in San Antonio, TX.
TechNow has developed a proven training program that brings the skillset to the certification process. TechNow is a mobile testing center that can deliver D0D 8570 training and the certification in one week. Our intergrated DoD 8570 training in San Antonio, TX incorporates hands on skills with testing objectives that produces an incredibly high pass rate. To learn more about our DoD 8570 training program click here

Course Overview:
This course explores the VMware Infrastructure, which consists of VMware ESX Server & VMware Virtual Center Server. We will look at both the design environments and operational processes of the VMware Infrastructure. This course provides IT architects with the insight needed to tackle tough issues in server virtualization such as virtual machine technologies, storage infrastructure, and designing clustered environments. Extensive hands-on labs provide for a rich student experience.
Attendees to VM-315: VMware Infrastructure: Install, Configure, and Manage will receive TechNow approved course materials and expert instruction.
Dates/Locations:
| Date/Time | Event |
|---|---|
|
03/24/2025 - 03/28/2025 08:00 -16:00 |
VM-315: VMware Infrastructure: Install, Configure, and Manage TechNow, Inc, San Antonio TX |
|
06/16/2025 - 06/20/2025 08:00 -16:00 |
VM-315: VMware Infrastructure: Install, Configure, and Manage TechNow, Inc, San Antonio TX |
|
09/29/2025 - 10/03/2025 08:00 -16:00 |
VM-315: VMware Infrastructure: Install, Configure, and Manage TechNow, Inc, San Antonio TX |
Duration: 5 Days
Course Objectives:
- Virtual Infrastructure Overview
- ESX and ESXi Server Installation
- Configuration of Networking, Scalability and Security
- Storage
- Install and Configure vCenter Server and Components
- Creation, Deployment, Management, and Migration of Virtual Machines
- Utilize vCenter Server for Resource Management
- Utilize vCenter Server for Virtual Machine Access Control and User Managment
- Use vCenter Server to increase scalability
- Monitoring Your Environment
- Data & Availability Protection Troubleshooting
-
Use VMware vCenter Update Manager to apply ESXi patches
-
Use vCenter Server to manage vMotion, HA, DRS and data protection.
Prerequisites:
- To ensure your success, system administration experience on Microsoft or Linux operating systems is required.
Comments
Latest comments from students
User: wolfdenise
Instructor comments: The instructor was nice and kept us entertained while providing instruction.
Facilities comments: The facility was nice, clean and easy to get to.
User: asteeves@aol.com
Instructor comments: knowledgeable but can get off subject at times
Facilities comments: good
Like the class? Then let everyone know!
Course Overview:
A rigorous Pen Testing program that, unlike contemporary Pen Testing courses, teaches you how to perform an effective penetration test across filtered networks. The course requires you to Pen Test IoT systems, OT systems, builds on your ability to write your own exploits, build your own tools, conduct advanced binaries exploitation, double pivot to access hidden networks, and various technologies.
What’s Included:
-
- EC-Council official E-Courseware
- EC-Council official Certificate of Attendance
- EC-Council iLabs with access for 6 months
- EC-Council CPENT Range access
- CEH Exam Voucher
Dates/Locations:
No Events
Duration: 5 days
Course Content:
-
- Module 01. Introduction to Penetration Testing
- Module 02. Penetration Testing Scoping and Engagement
- Module 03. Open Source Intelligence (OSINT)
- Module 04. Social Engineering Penetration Testing
- Module 05. Network Penetration Testing – External
- Module 06. Network Penetration Testing – Internal
- Module 07. Network Penetration Testing – Perimeter Devices
- Module 08. Web Application Penetration Testing
- Module 09. Wireless Penetration Testing
- Module 10. IoT Penetration Testing
- Module 11. OT/SCADA Penetration Testing
- Module 12. Cloud Penetration Testing
- Module 13. Binary Analysis and Exploitation
- Module 14. Report Writing and Post Testing Actions
Prerequisites:
Target Audience:
Penetration Testers, Ethical Hackers, Information Security Consultants/ Testers/ Analysts/ Engineers, Network Server Administrators, Firewall & System Administrators, Risk Assessment Professionals
Comments
Latest comments from students
Liked the class? Then let everyone know!
