Course Overview:
This CEH course will immerse you into a “Hacker Mindset” in order to teach you how to think like a hacker and better defend against future attacks. Students are in the driver’s seat with a hands-on training environment employing a systematic ethical hacking process. All while teaching students how to scan, test, hack, and secure target systems. CEH shows how hackers think and act maliciously so you can learn to better position your organization’s security infrastructure and defend against future attacks.
This CEH course covers the Five Phases of Ethical Hacking, diving into Reconnaissance, Gaining Access, Enumeration, Maintaining Access, and covering your tracks.
This CEH course delivers in-demand ethical hacking skills while preparing you for the internationally-recognized Certified Ethical Hacker (CEH) certification exam (312-50) from EC-Council.
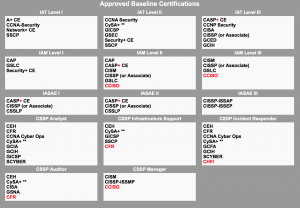
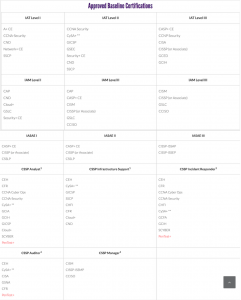
This course supports a certification that is DoD approved 8570 Baseline Certificate and meets DoD 8140/8570 training requirements.
What’s Included:
- EC-Council official E-Courseware
- EC-Council official iLabs code with access for 6 months
- EC-Council official Certificate of Attendance
- CEH Exam Voucher
Dates/Locations:
No Events
Duration: 5 Days
Course Content:
- Module 01. Introduction to Ethical Hacking
- Module 02. Foot-printing and Reconnaissance
- Module 03. Scanning Networks
- Module 04. Enumeration
- Module 05. Vulnerable Analysis
- Module 06. System Hacking
- Module 07. Malware Threats
- Module 08. Sniffing
- Module 09. Social Engineering
- Module 10. Denial-of-Service
- Module 11. Session Hijacking
- Module 12. Evading IDS,Firewalls, and Honeypots
- Module 13. Hacking Web Servers
- Module 14. Hacking Web Applications
- Module 15. SQL Injection
- Module 16. Hacking Wireless Networks
- Module 17. Hacking Mobile Platforms
- Module 18. IoT and OT Hacking
- Module 19. Cloud Computing
- Module 20. Cryptography
Prerequisites:
- Windows operating system and/or Linux operating system or other Unix-based OS
- TCP/IP protocols and implementation
- At least 2 years of IT security experience
- TN-325:Security+
Target Audience:
Information Security Analyst/Administrator, Information Assurance (IA) Security Officer, Information Security Manager/Specialist, Auditors, Security Professional, Site Admins, Penetration Testers, Red Team,Risk/Threat/Vulnerability Analyst, Individuals concerned about the integrity of network infrastructure
About us:
TechNow has taught security courses for almost 30 years, before most certifications existed and has successfully moved students through certification programs associated with IAPP, SANS, EC-Council and ISC2. Our instructor maintains over a dozen security certifications and has been the director of a company with internationals sales in security training, consulting, and compliance.

Tech Now, Inc. is an accredited Training Center with Ec-Council.
Comments
Latest comments from students