Here are the Information Privacy Protection course offerings:
Course Overview:
Through hands-on labs, you will learn to automate system administration tasks on managed hosts with Ansible, learn how to write Ansible playbooks to standardize task execution, and manage encryption for Ansible with Ansible Vault. This course will also teach you how to deploy and use Red Hat® Ansible Tower to centrally manage existing Ansible projects, playbooks, and roles; perform basic maintenance and administration of the Ansible Tower installation; and configure users and teams and use them to control access to systems, projects, and other resources through role-based access controls. You will learn to use Ansible Tower’s visual dashboard to launch, control, and monitor Ansible jobs; use the Ansible Tower application programming interface (API) to launch jobs from existing templates; automatically schedule Ansible jobs; and dynamically update host inventories.
Course Objectives:
- Install and troubleshoot Ansible on central nodes and managed hosts
- Automate administration tasks with Ansible playbooks and ad hoc commands
- Write effective Ansible playbooks
- Protect sensitive data used by tasks with Ansible Vault.
- Install and configure Ansible Tower for enterprise Ansible management
- Use Ansible Tower to control access to inventories and machine credentials by users and teams
- Create job templates in Ansible Tower to standardize playbook execution.
- Centrally launch playbooks and monitor and review job results with Ansible Tower
Course Outline:
- Introduce Ansible
- Deploy Ansible
- Implement playbooks
- Manage variables and inclusions
- Implement task control
- Implement Jinja2 templates
- Implement roles
- Configure complex playbooks
- Implement Ansible Vault
- Troubleshoot Ansible
- Install Ansible Tower and describe Ansible Tower’s architecture
- Create users and teams for role-based access control
- Create and manage inventories and credentials
- Manage projects for provisioning with Ansible Tower
- Construct advanced job workflows
- Update inventories dynamically and compare inventory members
- Maintenance and administration of Ansible Tower
Dates/Locations:
No Events
Duration: 5 Days
Prerequisites:
- Become a Red Hat Certified System Administrator, or demonstrate equivalent experience
Target Audience:
This course is designed for Linux system administrators, cloud administrators, and network administrators needing to automate configuration management, application deployment, and intraservice orchestration at an enterprise scale.
Course Overview:
A rigorous Pen Testing program that, unlike contemporary Pen Testing courses, teaches you how to perform an effective penetration test across filtered networks. The course requires you to Pen Test IoT systems, OT systems, builds on your ability to write your own exploits, build your own tools, conduct advanced binaries exploitation, double pivot to access hidden networks, and various technologies.
What’s Included:
-
- EC-Council official E-Courseware
- EC-Council official Certificate of Attendance
- EC-Council iLabs with access for 6 months
- EC-Council CPENT Range access
- CEH Exam Voucher
Dates/Locations:
No Events
Duration: 5 days
Course Content:
-
- Module 01. Introduction to Penetration Testing
- Module 02. Penetration Testing Scoping and Engagement
- Module 03. Open Source Intelligence (OSINT)
- Module 04. Social Engineering Penetration Testing
- Module 05. Network Penetration Testing – External
- Module 06. Network Penetration Testing – Internal
- Module 07. Network Penetration Testing – Perimeter Devices
- Module 08. Web Application Penetration Testing
- Module 09. Wireless Penetration Testing
- Module 10. IoT Penetration Testing
- Module 11. OT/SCADA Penetration Testing
- Module 12. Cloud Penetration Testing
- Module 13. Binary Analysis and Exploitation
- Module 14. Report Writing and Post Testing Actions
Prerequisites:
Target Audience:
Penetration Testers, Ethical Hackers, Information Security Consultants/ Testers/ Analysts/ Engineers, Network Server Administrators, Firewall & System Administrators, Risk Assessment Professionals
Comments
Latest comments from students
Liked the class? Then let everyone know!

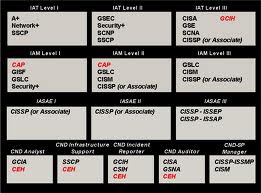
DoD 8570 Training in San Antonio, TX.
TechNow has developed a proven training program that brings the skillset to the certification process. TechNow is a mobile testing center that can deliver D0D 8570 training and the certification in one week. Our intergrated DoD 8570 training in San Antonio, TX incorporates hands on skills with testing objectives that produces an incredibly high pass rate. To learn more about our DoD 8570 training program click here
Course Overview:
This course is designed for students who intend to work with virtual private networks (VPNs) using IPSec. The course includes detailed coverage of the VPN 3000 Concentrator, a scalable remote access platform that offers encryption, high availability, and superior performance. This class is an invaluable theory and configuration guide for the VPN 3000 series of products, with its thorough coverage of concentrators, hardware clients, and software clients.
Attendees to N-315: Cisco Secure Virtual Private Networks will receive TechNow approved course materials and expert instruction.
Dates/Locations:
No Events
Duration: 5 days
Course Objectives:
- Network Security & Virtual Private Network Technologies Cisco VPN 3000 Concentrator Series Hardware Overview
- Routing on the VPN 3000
- Configuring the Cisco VPN 3000 for Remote Access Using Pre-shared Keys
- Configuring the Cisco VPN 3000 for Remote Access Using Digital Certificates
- The Cisco VPN Client Firewall Feature
- Configuring the Cisco 3002 Hardware Client for Remote Access
- Configuring the Cisco 3002 Hardware Client for User & Unit Authentication
- Configuring Cisco VPN Clients for Backup Server, Load Balancing & Reverse Route Injection
- Configuring the Cisco 3000 Concentrator for IPSec over TCP & UDP
- Configuring LAN-to-LAN VPNs on the Cisco 3000
- Network Monitoring & Administration Troubleshooting
Prerequisites:
- Students who attend this advanced course must have experience in configuring Cisco IOS software
- CCNA certification
- Basic knowledge of the Windows operations system
- Familiarity with the networking & security terms & concepts
Comments
Latest comments from students